Expiring Credit Card Rewards: A Phishing Scam Breakdown
I. Introduction
This weekend I received a message informing me that I had credit card points about to expire.
I had always wanted to analyze this type of attack but had not been able to obtain an active link. I then checked other phones nearby and observed that they had received the same message in the same format, suggesting that this may have been distributed using an IMSI catcher.
After returning home, I analyzed the links, messages and conducted research. Since there wasn’t any detailed analysis of this scam publicly available, I decided to create one.
The goal of this analysis is to document the scam’s characteristics and provide Indicators of Compromise (IOCs) to help prevent similar incidents in the future.
II. Incident Overview
| Field | Details |
|---|---|
| Scam Type | Text Hijacking |
| Target | Customers of Legitimate Banks |
| Delivery Method | SMS |
| Device Used | IMSI Catcher |
| Objective | Credential harvesting |
💡Text hijacking, also known as spoofing, is a scam where fraudsters send messages that appear to originate from trusted sources. These messages often use the very same names of banks and legitimate companies to trick recipients into revealing sensitive information or transferring funds. [1]
III. SMS Message Analysis
Message Metadata
| Attribute | Value |
|---|---|
| Message Type | SMS |
| Date Observed | March 7, 2026 |
Message Content
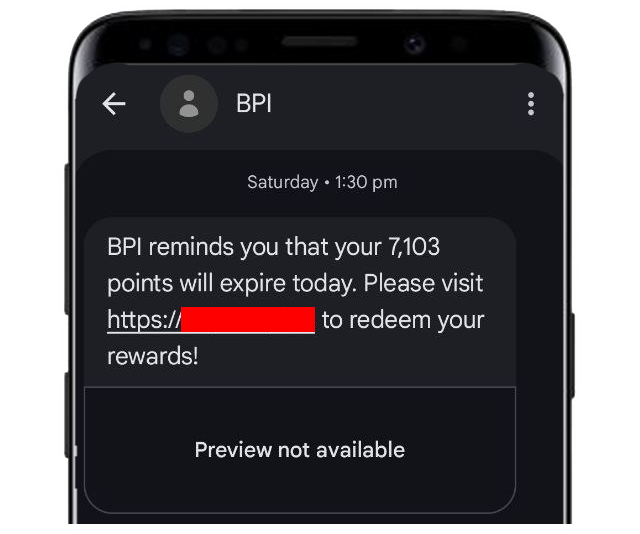
# Gathered Message Samples
- "{BANK} reminds you that your {POINTS_AMOUNT} points will expire today. Please visit {LINK} to redeem your rewards!"
- "{BANK} rewards: Congratulations! You have a pending {POINTS_AMOUNT} CASH BACK. This offer is exclusively for BPI Credit Cardholders. Claim now at: {LINK}"
- "{BANK} would like to remind you that {POINTS_AMOUNT} points in your bank account will expire today. Redeem your rewards now! Visit {LINK} to redeem your points."
- "Your credit card points will expire in 5 hours. You will lose your chance to get {POINTS_AMOUNT} pesos cashback. Redeem now: {LINK}"
- "{BANK} reminds you that your rewards points {POINTS_AMOUNT} will expire today. Please visit to redeem your favorite gift: {LINK}"
- "Surprise! Your {POINTS_AMOUNT} {BANK} cash rebate is here. We're trully thankful for your continued support and every tansaction. Enjoy it - celebrate or save toward your goals: "Analysis
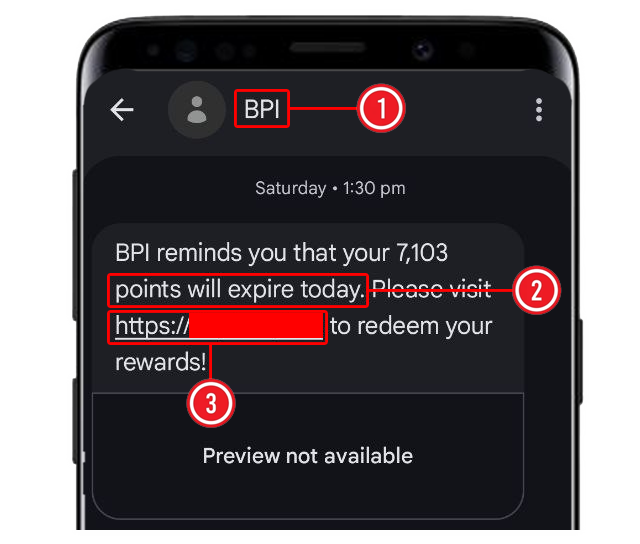
- The sender ID is spoofed to appear legitimate.
- Urgency is introduced through threats of points expiration.
- The message includes a malicious link containing the legitimate domain but contains subtle variations, designed to redirect victims to a phishing page.
What is an IMSI catcher? What is its purpose?
International Mobile Subscriber Identity (IMSI) catchers are devices used to carry out text hijacking. These devices broadcast a stronger signal than nearby legitimate cellular towers, tricking mobile phones in a specific area into connecting to them instead of the real network. [2]
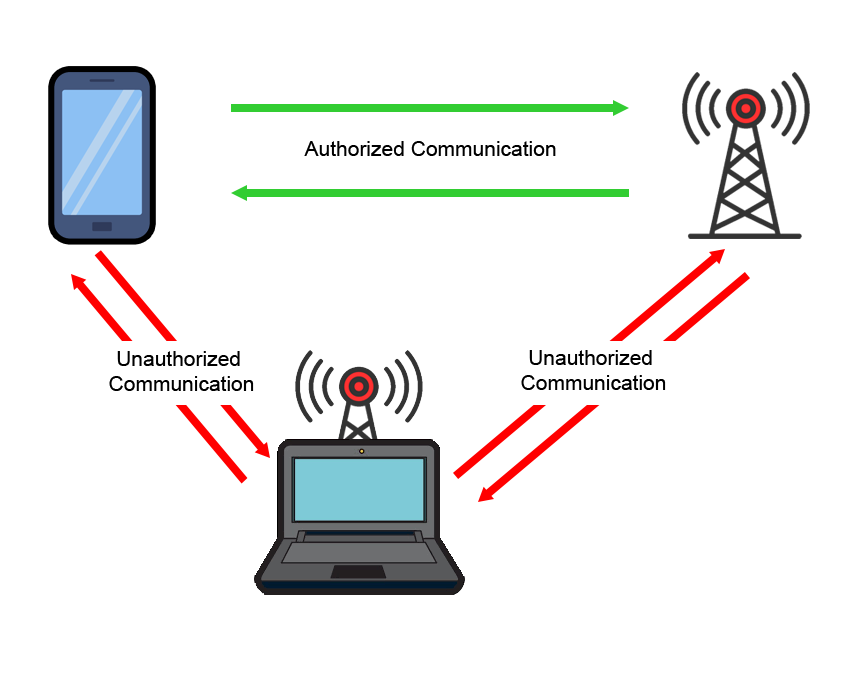
Once connected, attackers can send SMS or text messages containing malicious content or phishing links, potentially compromising sensitive information.
Reportedly, such devices are transported in the back of cars roaming around Manila, enabling attackers to target mobile users on the move.
IMSI Catcher Indicators
Possible signs that the message may have been transmitted via an IMSI catcher:
- Sudden broadcast SMS messages received simultaneously by multiple devices.
- Messages appearing from a trusted sender ID with a valid conversation history.
IV. Malicious Link Analysis
⚠️ Note: The links listed below may be harmful. Do NOT click, open or interact with them. This report is provided solely for informational and security awareness purposes.
| Attribute | Value |
|---|---|
| URL | hxxps://bpl-2r2[.]com/ph |
| Domain Registration | 2026-03-07 |
Observations
- Domain is recently registered (4 days old)
- Domain used the following trackers to monitor visitor behavior, track clicks and potentially improve the effectiveness of the scam.
- Google Tag Manager (GTM)
- Quantcast (quant.js)
- Twitter Ads (uwt.js)
- Facebook Connect
- AppNexus (pixie.js)
- Domain copies the original metadata values of the fields below from the original website. (Title, og:type, og:description, og:title, template, keywords, twitter:title, twitter:card, twitter:description)
Dynamic Analysis
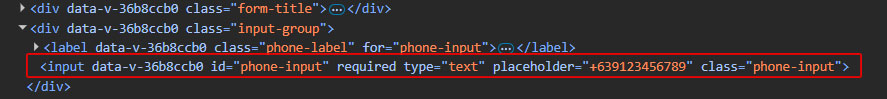
Upon opening the link, the user is prompted to enter their mobile number.

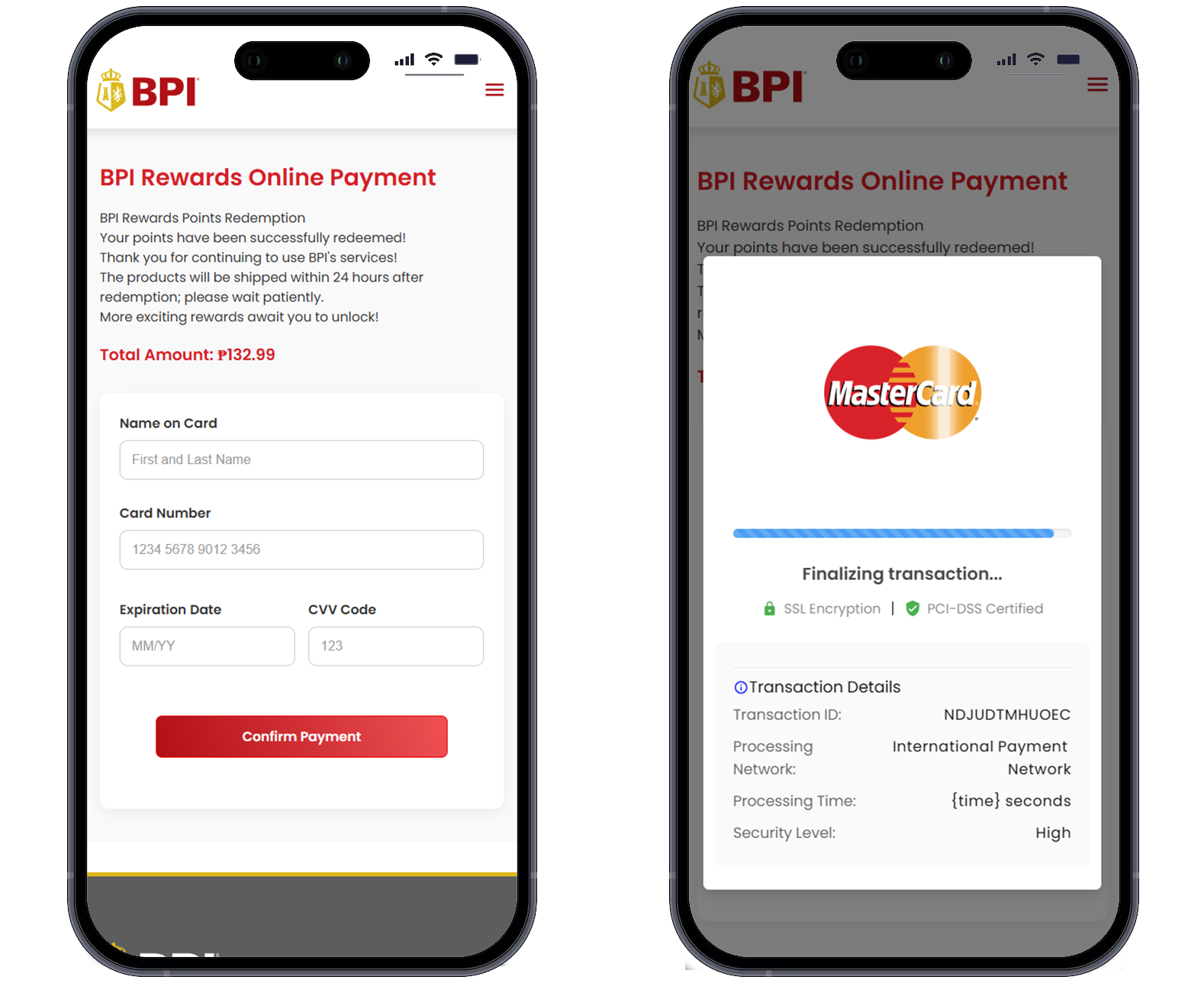
The field is required; however, the input type is set to text instead of tel, which allows the form to proceed even if letters are entered.
After submission, an information page appears. Checking the source code of this page shows that it is highly obfuscated.

The page states that reward points are expiring with urgency and encourages the victim to claim them. It provides steps on how to redeem the points and displays important notes regarding the redemption process. The page is very convincing and well designed.
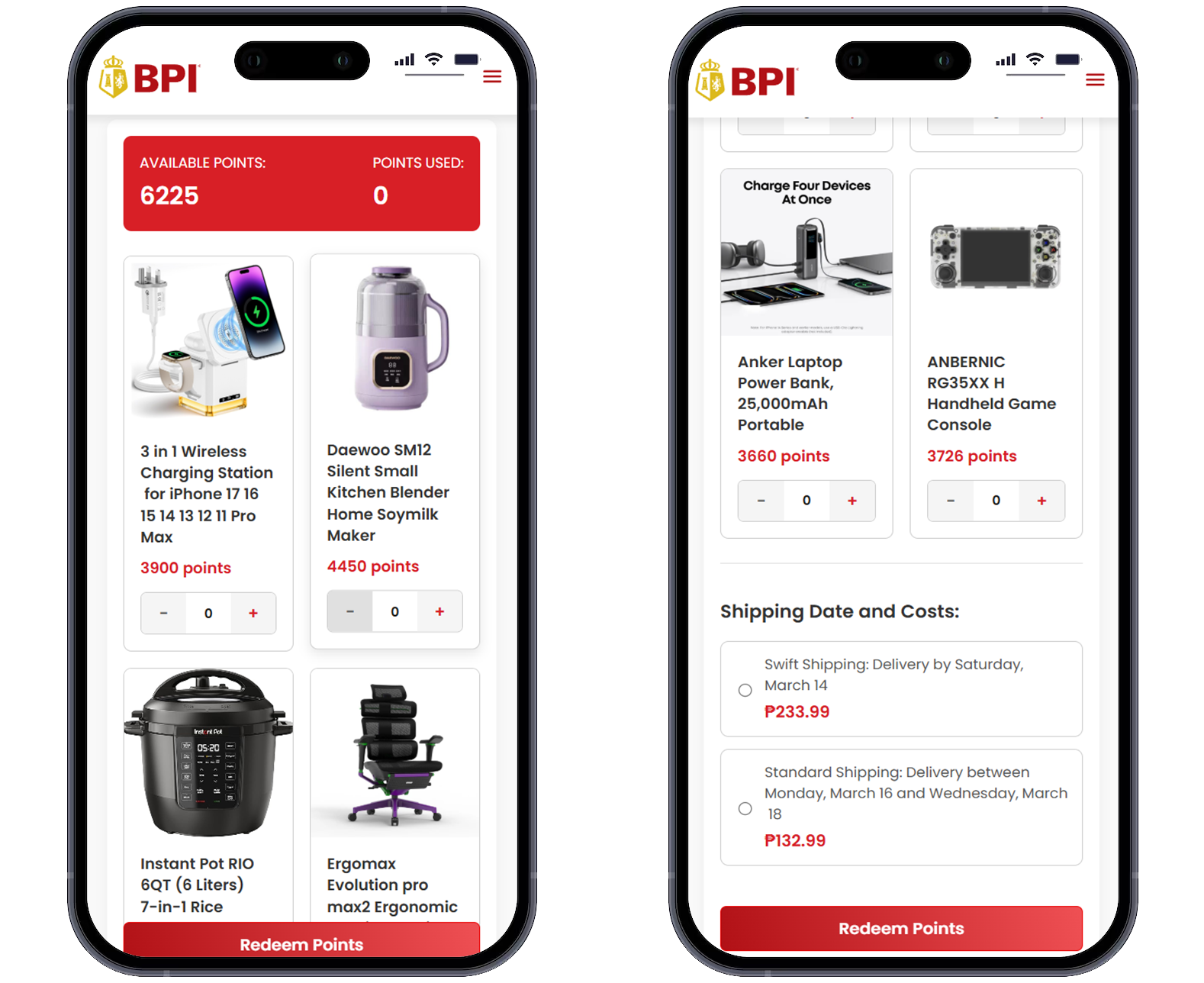
After clicking Continue, the system will display the items available for claiming based on the current points balance. After choosing an item, two shipping options are available at the bottom of the page: Swift Shipping and Standard Shipping. These options are intended to make the process appear legitimate. However, they are also used as a reason to ask for the victim’s credit card information.
It will then ask for the shipping address and proceed to the payment screen. Once you enter your card details, it will ask for the OTP. You will then be charged an amount that is more than the supposed shipping fee. After the transaction, you will be redirected to the official BPI website.
V. Indicators of Compromise (IOCs)
URLs
# Gathered URLs
#BPI
- `hxxps://bpl-2r2[.]com/ph`
- `hxxps://finph-bpi[.]cc`
- `hxxps://bpi-oph[.]com`
- `hxxps://bimaioczl[.]cc/ph`
- `hxxps://bpionvertt[.]com/ph`
- `hxxps://rewardx-bpi[.]com`
- `hxxps://bpi-er1t[.]info[.]ph`
#BDO
- `hxxps://bdo[.]com-ph[.]cc/`
- `hxxps://bdo-pmo[.]cc/`
- `hxxps://bdo-card[.]com/`
#GLOBE
- `hxxps://globemo-ph[.]com`
#EASTWEST
- `hxxps://eastwest-cph[.]com`VI. Conclusion
This campaign demonstrates a SMS phishing attack impersonating legitimate banks, potentially delivered via IMSI catcher. The combination of spoofed sender IDs, urgency tactics and a convincing phishing website increases the likelihood of successful credential harvesting.
Continuous monitoring of suspicious domains and SMS patterns, along with raising awareness, can help prevent further activity from this campaign.
Recommendations
- Do not click links received via SMS claiming to be from banks.
- Always access banking services through official applications or known domains.
- Report any unusual transactions or activities involving your bank or e-money accounts to your bank or e-money provider immediately.
Read More
- Maya - What Is Text Hijacking or Spoofing and How Can You Protect Yourself?
- BDO - Banking public warned against prevalence of text or SMS hijacking scam
- BPI - Things To Do When Getting Suspicious Messages
- Metrobank - How to fight fraud by spotting a fake SMS
References
[1]https://www.maya.ph/stories/what-is-text-hijacking-or-spoofing-and-how-can-you-protect-yourself [2]https://www.bsp.gov.ph/SitePages/MediaAndResearch/MediaDisp.aspx?ItemId=7360
Feel free to reach out via leekristiancao@gmail.com if you have questions, suggestions or need more details about this analysis.